 I gave the well-received presentation “Deprecating the Password: A Progress Report” at the May 2018 European Identity and Cloud Conference (EIC). The presentation is available as PowerPoint (large because of the embedded video) and PDF.
I gave the well-received presentation “Deprecating the Password: A Progress Report” at the May 2018 European Identity and Cloud Conference (EIC). The presentation is available as PowerPoint (large because of the embedded video) and PDF.
The presentation abstract is:
If you ask almost anyone you meet if they have too many passwords, if they have trouble remembering their passwords, or if they are reusing the same passwords in multiple places, you’re likely to get an ear-full. People intuitively know that there has to be something better than having to have a password for everything they do!
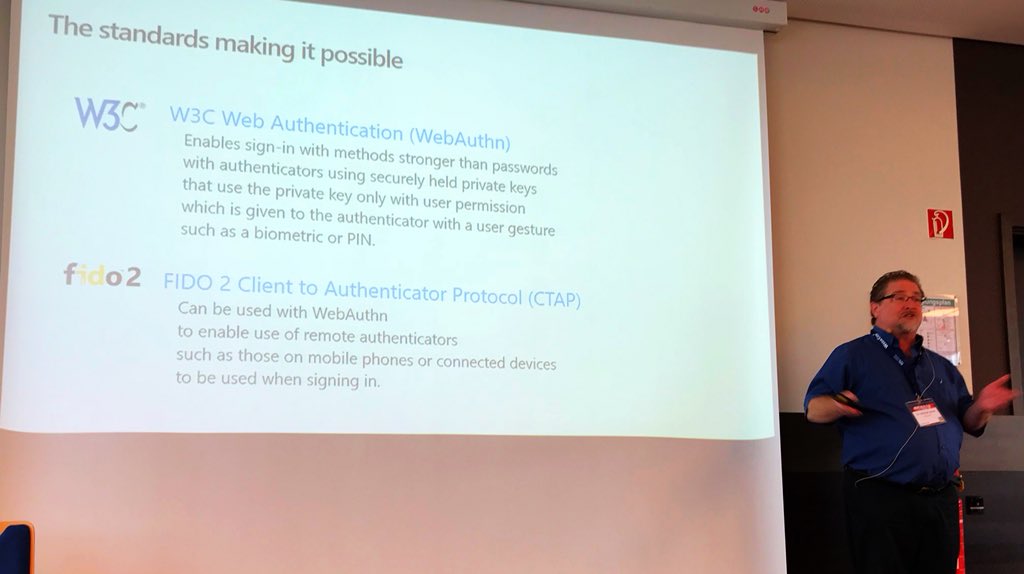
The good news is that passwords are being used for fewer and fewer identity interactions. They are being replaced by biometrics (sign into your phone, your PC, or your bank with your face or fingerprint), local PINs (prove it’s you to your device and it does the rest), and federation (sign in with Facebook, Google, Microsoft, etc.). This presentation will examine the progress we’ve made, the standards and devices making it possible, and stimulate a discussion on what’s left to do to deprecate the password.
Key takeaways are:
-
There are good alternatives to passwords in use today.
Passwords are being used for fewer and fewer identity interactions.
Devices are increasingly enabling authentication without passwords.
New standards are enabling cross-platform password-less authentication.
The days of having to use passwords for everything you do are numbered!
Thanks to Steve Hutchinson for this photo from the presentation and his vote of confidence.
Extra: See all the Microsoft presentations at EIC 2018, including videos of Joy Chik’s and Kim Cameron’s keynotes.













