I wanted to bring your attention to two whitepapers covering important Internet identity topics that were published by members of Microsoft’s Trustworthy Computing and Privacy teams, both announced on the blog The Data Privacy Imperative.
The first is “Online Identity Theft: Changing the Game — Protecting Personal Information on the Internet” by Jules Cohen, Brendon Lynch, and other members of Microsoft’s Trustworthy Computing team. Per the announcement, the paper:
… for the first time describes in detail Microsoft’s comprehensive strategy for curbing online identity theft. In addition to describing current Microsoft initiatives, the paper outlines long-term solutions for “changing the game” by ending reliance on “shared secrets” for authentication.
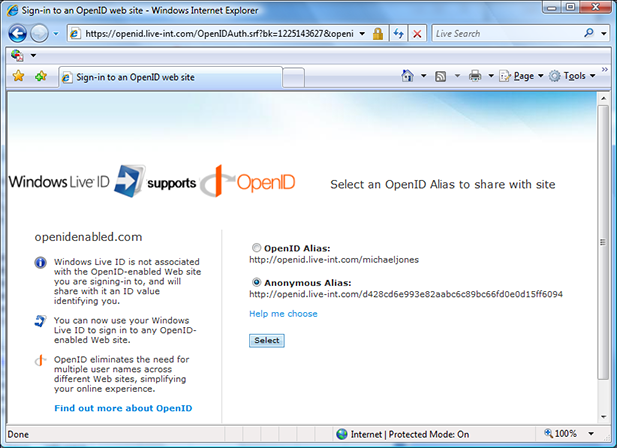
Relying on “shared secrets,” such as usernames, passwords, birthdates and government ID numbers to establish the right to do something online, creates security problems because they are relatively easy to steal and can be difficult to remember, update and manage. We need to employ new identity practices online that are just as reliable but better protect against fraud and abuse, and that’s where Information Cards come in …
The paper has been greeted by favorable reviews, including an Information Week article that also describes the role that the Information Card Foundation can play and a NetworkWorld article by Dave Kearns that concludes “Download this important paper, read it, then act on it.”
The second is “Digital Playgrounds: Creating Safer Online Environments for Children” by Jules Cohen of Microsoft’s Trustworthy Computing team and Chuck Cosson, Policy Counsel on privacy and safety issues, with some input from me. The paper was presented to the Internet Safety Technical Task Force (ISTTF) by Jules and submitted by Microsoft as input to the task force. As Jules wrote about the approach:
The Digital Playgrounds paper outlines a framework that would enable the creation of optional online “walled gardens,” specifically for children and trusted adults. These online sites would only be accessible by folks with trusted and age verified ‘digital identities.’ This framework suggests achieving this by allowing trusted offline parties, who have the ability to meet with a parent and child in real life, examine the appropriate documents and then issue extremely secure digital identities based on these in in-person proofing moments. The framework we have outlined is largely a technical solution to the age verification challenge, but we believe that the nontechnical aspects of the problem will be as difficult to solve as the technical ones, if not more so. For example, government and industry will need to work together on designing the necessary criteria for in-person proofing events as well as the subsequent issuing, auditing and revoking of these digital identity cards.
I especially encourage people to consider the possibility that existing offline identity proofing ceremonies might be leveraged to enhance safety online as well.
 I’m excited that the first beta of the next version of CardSpace — Windows CardSpace “Geneva” — is now available. You can download the bits for this and the other “Geneva” betas at the “Geneva” Connect site. The team posted a detailed introductory piece about the new version on the team blog, so I won’t repeat that here.
I’m excited that the first beta of the next version of CardSpace — Windows CardSpace “Geneva” — is now available. You can download the bits for this and the other “Geneva” betas at the “Geneva” Connect site. The team posted a detailed introductory piece about the new version on the team blog, so I won’t repeat that here.